Authored by Michael Snyder via The Economic Collapse blog,
As far as Big Brother is concerned, nothing that you do on your cell phone is ever private. And if the government really wants to see what is on your cell phone,
they are going to get that information one way or another, even if that means resorting to physical violence. On Monday,
NBC News
provided us with yet another glaring example of how the United States
is being transformed into a Big Brother police state. On January 1st,
Akram Shibly and Kelly McCormick from Buffalo, New York were coming back
home from a trip to Toronto, and they didn’t anticipate any unusual
problems when they got to the border. Unfortunately for them, U.S.
Customs & Border Protection agents decided to take their cell
phones, demanded their passwords, and kept them in custody for the next
two hours as they searched for anything that might be incriminating on
those phones.
You might be thinking that sounds like it
should be
illegal, and you would be correct, but sadly federal courts have ruled
that our constitutional rights do not apply to border searches. So
authorities use this legal loophole to do pretty much anything they want
at the border.
If that young couple from Buffalo would have had something illegal on
their phones, they could have been immediately arrested and put in
prison.
And we haven’t even gotten to the worst part of the story yet. Just a
few days later Akram Shibly and Kelly McCormick took another trip to
Canada, and this time border agents physically assaulted Akram when he
did not immediately turn over his phone. The following comes from
NBC News…
Three days later, they returned from another trip to Canada and were stopped again by CBP.
“One of the officers calls out to me and says, ‘Hey, give me your
phone,'” recalled Shibly. “And I said, ‘No, because I already went
through this.'”
The officer asked a second time.
Within seconds, he was surrounded: one man held his legs,
another squeezed his throat from behind. A third reached into his
pocket, pulling out his phone. McCormick watched her boyfriend’s face
turn red as the officer’s chokehold tightened.
Is this still America?
I can’t believe that this is what the United States has become. When
I was young I remember reading about this sort of thing in Nazi
Germany, the USSR and Communist China, but I never imagined that it
would happen here. For years
I have been warning
about this growing “Big Brother police state control grid”, and I wish
that more Americans would realize how evil all of this government
surveillance truly is.
You can watch an interview where this couple from Buffalo talks to NBC News about this recent incident at the border
right here.
It is so disgusting that this is how we are treating law
abiding people when countless numbers of drug dealers and gang members
are pouring across unprotected sections of our border every single day.
Unfortunately, cell phone searches at the border appear to be rising at an exponential rate. According to
NBC News, more cell phone searches were conducted at the border during the month of February 2017 than in the
entire year of 2015…
Data provided by the Department of Homeland Security shows that searches of cellphones by border agents has exploded, growing fivefold in just one year, from fewer than 5,000 in 2015 to nearly 25,000 in 2016.
According to DHS officials, 2017 will be a blockbuster year. Five-thousand devices were searched in February alone, more than in all of 2015.
And of course it isn’t just searches at the border that you need to be concerned about.
Not too long ago, it was being reported that the CIA has helped the
Justice Department with technology that allows law enforcement officials
to scan
“data from thousands of U.S. cellphones at a time” from the safety of a plane…
The Central Intelligence Agency played a crucial role in helping the Justice Department develop technology that scans data from thousands of U.S. cellphones at a time,
part of a secret high-tech alliance between the spy agency and domestic
law enforcement, according to people familiar with the work.
The CIA and the U.S. Marshals Service, an agency of the Justice
Department, developed technology to locate specific cellphones in the
U.S. through an airborne device that mimics a cellphone tower, these
people said.
So the next time a strange plane flies over your house, this may be what is happening.
Here is more
on this disturbing new technology…
The
program operates specially equipped planes that fly from five U.S.
cities, with a flying range covering most of the U.S. population. Planes
are equipped with devices—some past versions were dubbed “dirtboxes” by
law-enforcement officials—that trick cellphones into reporting their
unique registration information.
I have a feeling that if this program was ever challenged in court
that it would be ruled unconstitutional, so let’s hope that happens as
soon as possible.
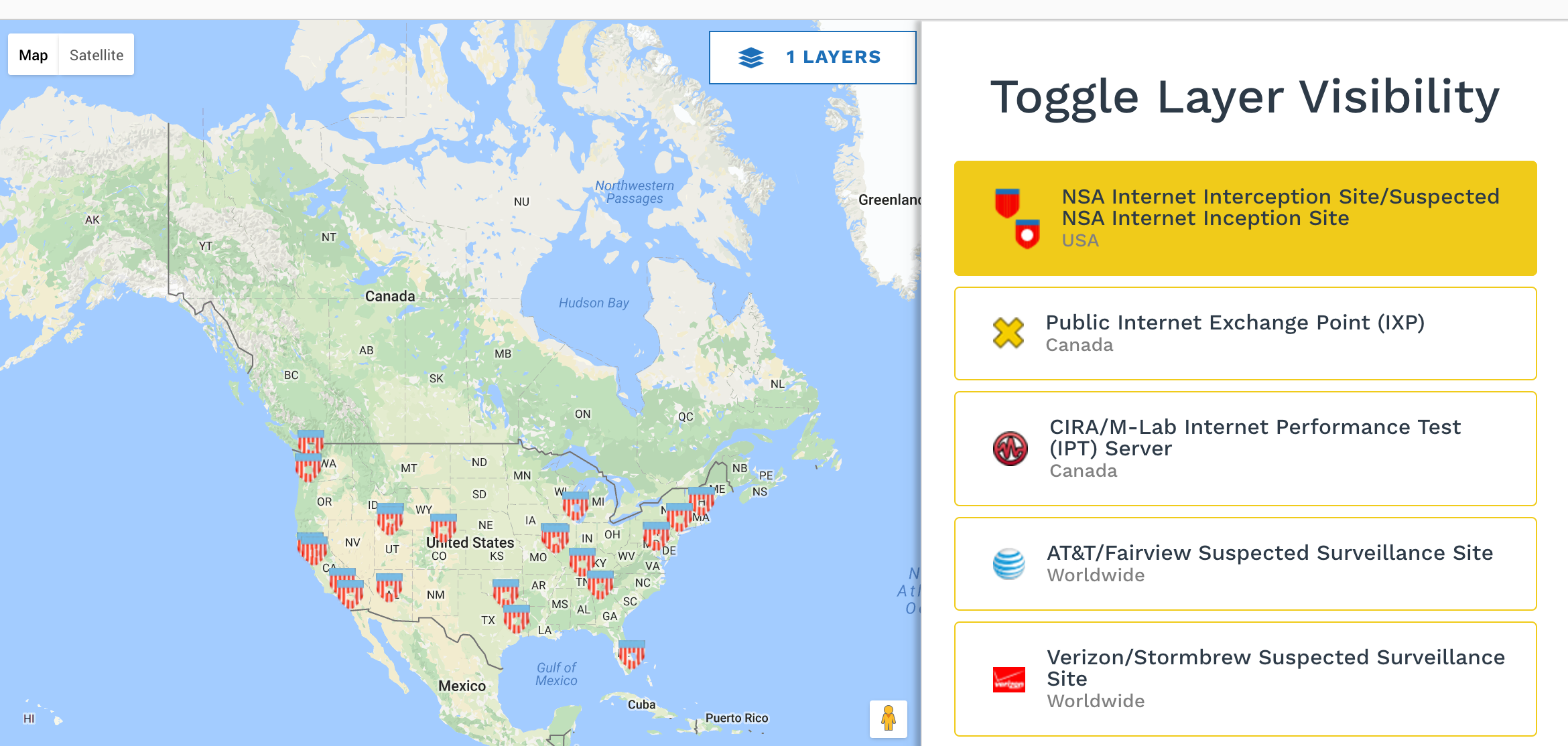
But then again, the NSA has been collecting and storing all forms of electronic communication for years and nothing is being done about.
We have even had a 36-year veteran of the NSA named William Binney come
out and publicly admit that all of our phone conversations “
are being monitored and stored” and still nothing is done to stop it.
So don’t do anything on your cell phone that you wouldn’t want the
government to see, because someday they could use it to nail you.
Of course we also need to use discretion regarding the things that we know the public will be able to see.
When you post something to Facebook or Twitter, you may think that it is harmless, but it could end up costing you big time. In fact, I just came across an article about how a number of pastors have actually been fired
because of what is on their social media accounts…
“It’s not fair I lost my job,” the pastor told me.
“My church members post a lot worse things than I do on social media. It’s a double standard.”
He’s right. It is a double standard. But it’s reality. And, with
greater frequency, more pastors and church staff are losing their jobs
because of what they post, particularly on Facebook and Twitter and, to
some extent, their blogs.
By the way, churches will not always tell the pastor the specific
reason for the firing. But, once we begin to infuriate our church
members with our posts, many will find a myriad of reasons to give us
the boot.
Like the title to this article says, what you do on your cell phone could come back to haunt you.
For many Americans, cell phones have become an essential part of modern life, but the truth is that those little electronic devices can also destroy our lives if we are not careful.
So if you are going to use them, use them wisely, because people are watching.